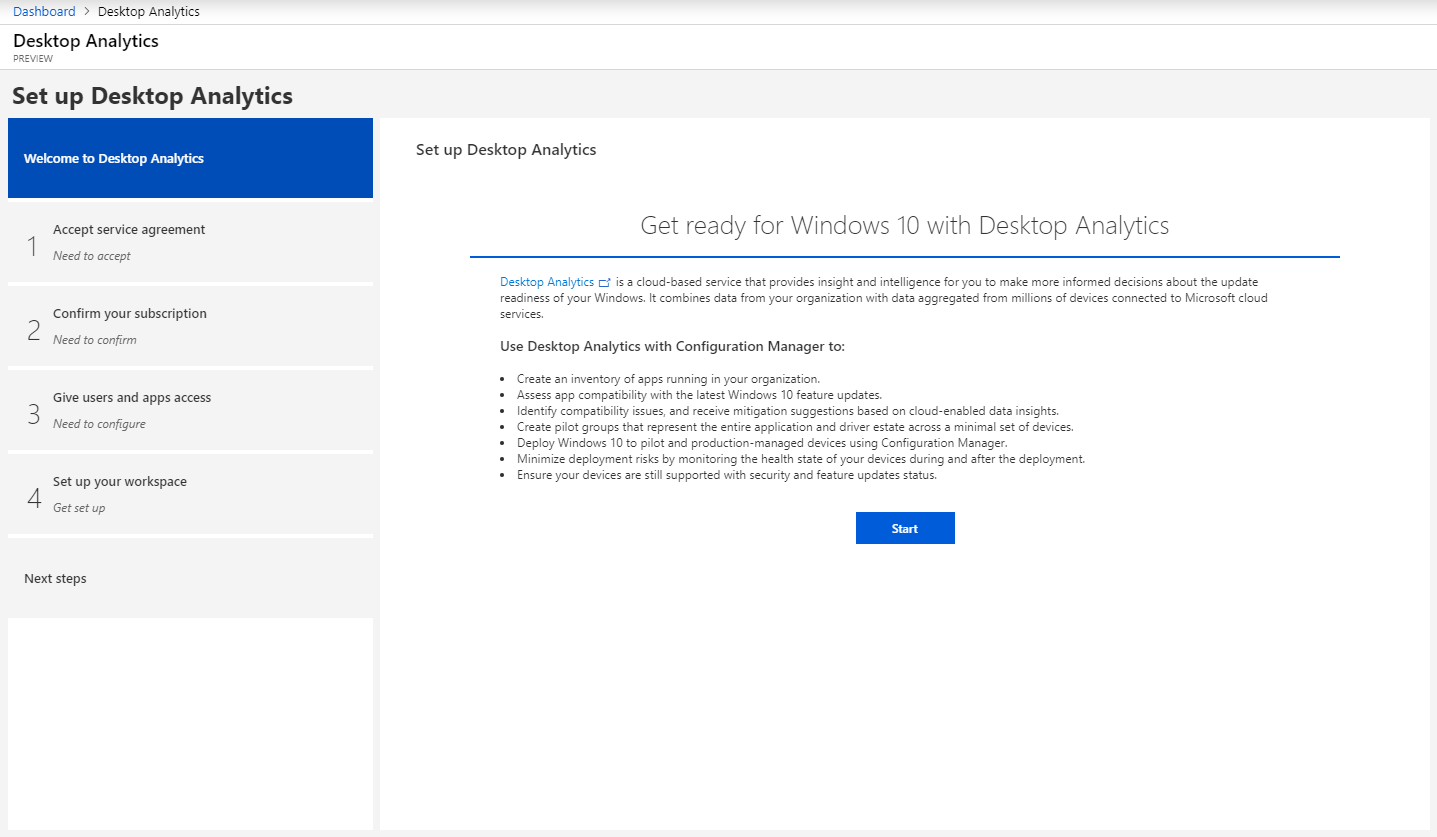
Microsoft goes new ways with Windows Analytics Upgrade Readiness, it is planned to discontinue the service by 31.01.2020. But there is a successor: “Desktop Analytics”. In July the preview for this service was announced, for Germany, this service is still only available in the preview. But there are some pitfalls and disadvantages for some customers, unfortunately.
At the moment these are all just public reflections and preview versions, as time will tell.