Behind the feature “Automatic Virtual Machine Activation” is a function in Microsoft Windows Server 2012R2 Datacenter, Microsoft Windows Server 2016 Datacenter and Microsoft Windows Server 2019 Datacenter for Hyper-V, but it works only with the Datacenter Edition activated. With this feature, all supported Windows Server operating systems since Microsoft Windows Server 2012R2 can be automatically activated by the Hyper-V host. But only up to the own version, which means that a Windows Server 2012 R2 Datacenter Hyper-V cannot activate Windows Server 2016. The limitation of this feature to the Datacenter Edition is due to the unlimited Virtual Windows Server Guests covered by the Datacenter License. The advantage is that it is now easier to assign the license to the corresponding datacenter license during a software audit on the AVMA license key.
Microsoft
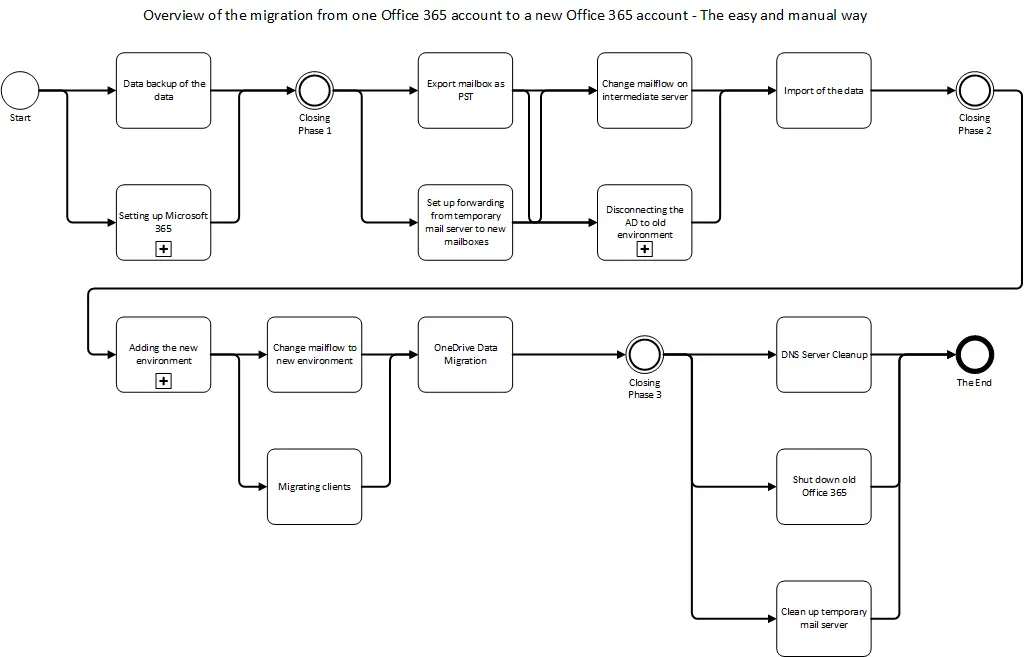
Migration from an Office 365 to a new Microsoft 365 Tenant – The approaches to migration
As MCT, I have a developer tenant for Office 365, and this year we are finally getting access to the Microsoft 365 function, i.e. Enterprise Mobility and Security. The disadvantage is that a new tenant is required and so a migration is pending. But at the same time, a lot of things have to be set up from scratch. I take the opportunity to write a series of blog posts directly from this.
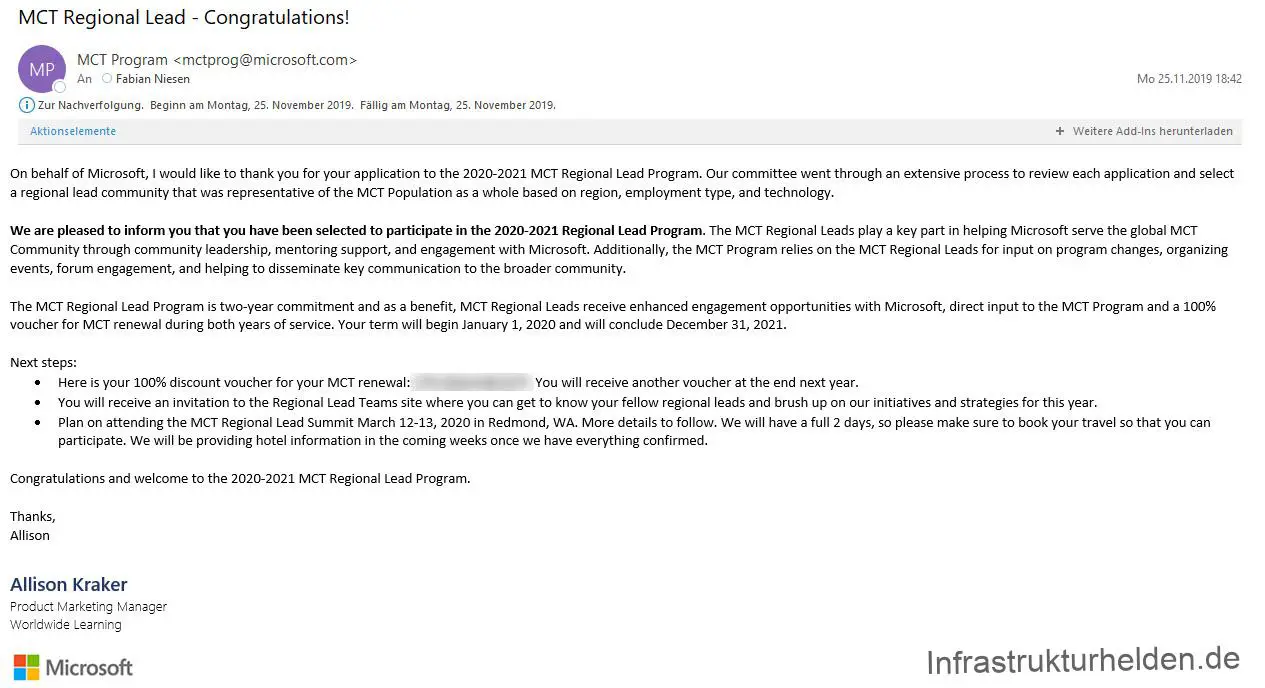
MCT Regional Lead 2020-2021
I got a mail from Microsoft, I was elected as an MCT Regional Lead for the 3rd time in a row. Since 2016 I am an MCT Regional Lead in Germany for Microsoft Certified Trainers.
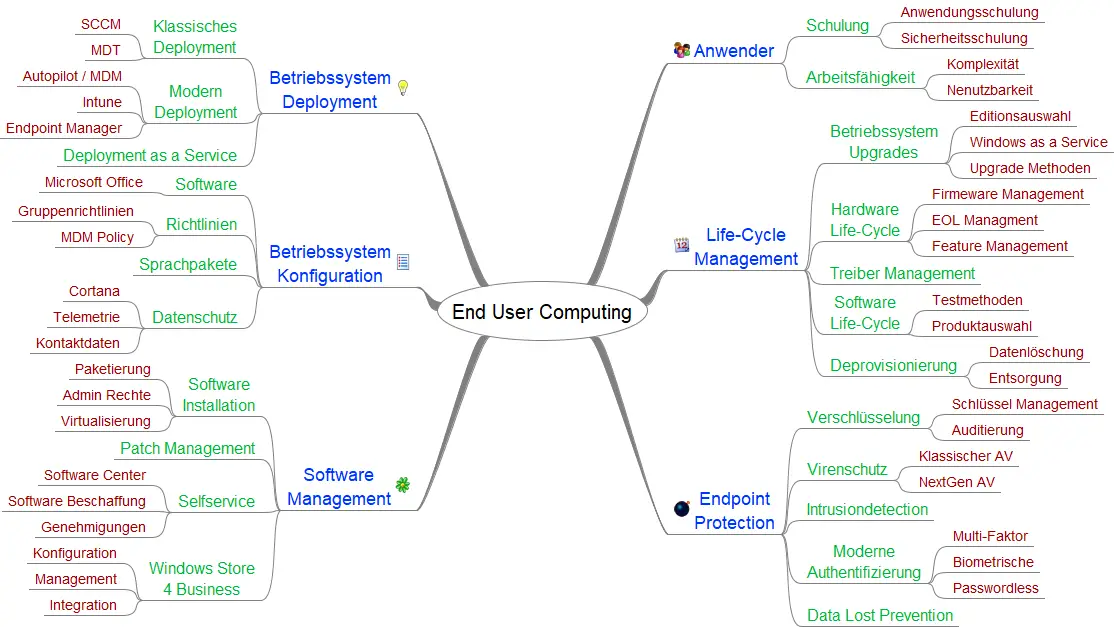
End User Computing MeetUp – Bonn / Koblenz Area (Germany)
For a long time, I have been planning a MeetUp on the topic of End User Computing, which I am starting to organize and regularly offering now. Many can’t imagine much about End-User Computing (EuC), in general, it’s about working on the end device, i.e. the computer, tablet, mobile phone and Co.
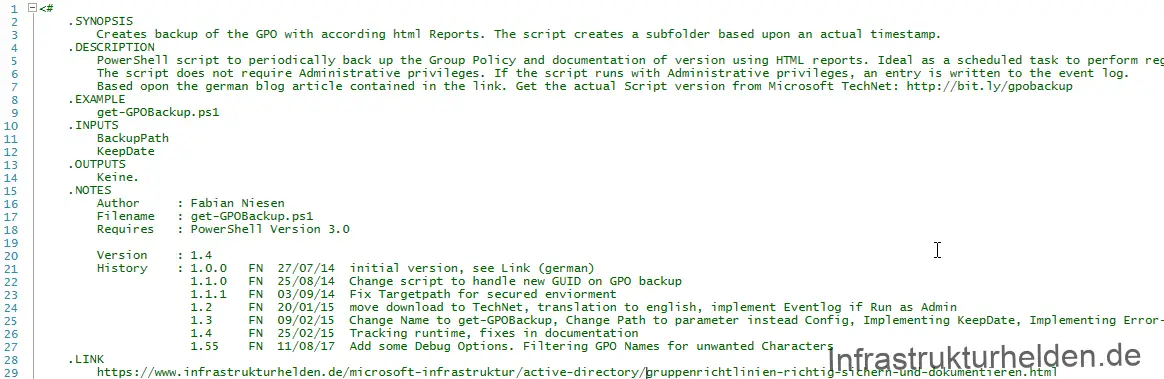
Properly secure and document group policies
It’s been some time since I started working on the first basic version of the script in August 2014, and posted about it on CONET’s blog. This first version came to just 6 lines of code without the header. Since then a lot has happened and the script has grown in the TechNet Gallery. Time for a new article about the script and its function.
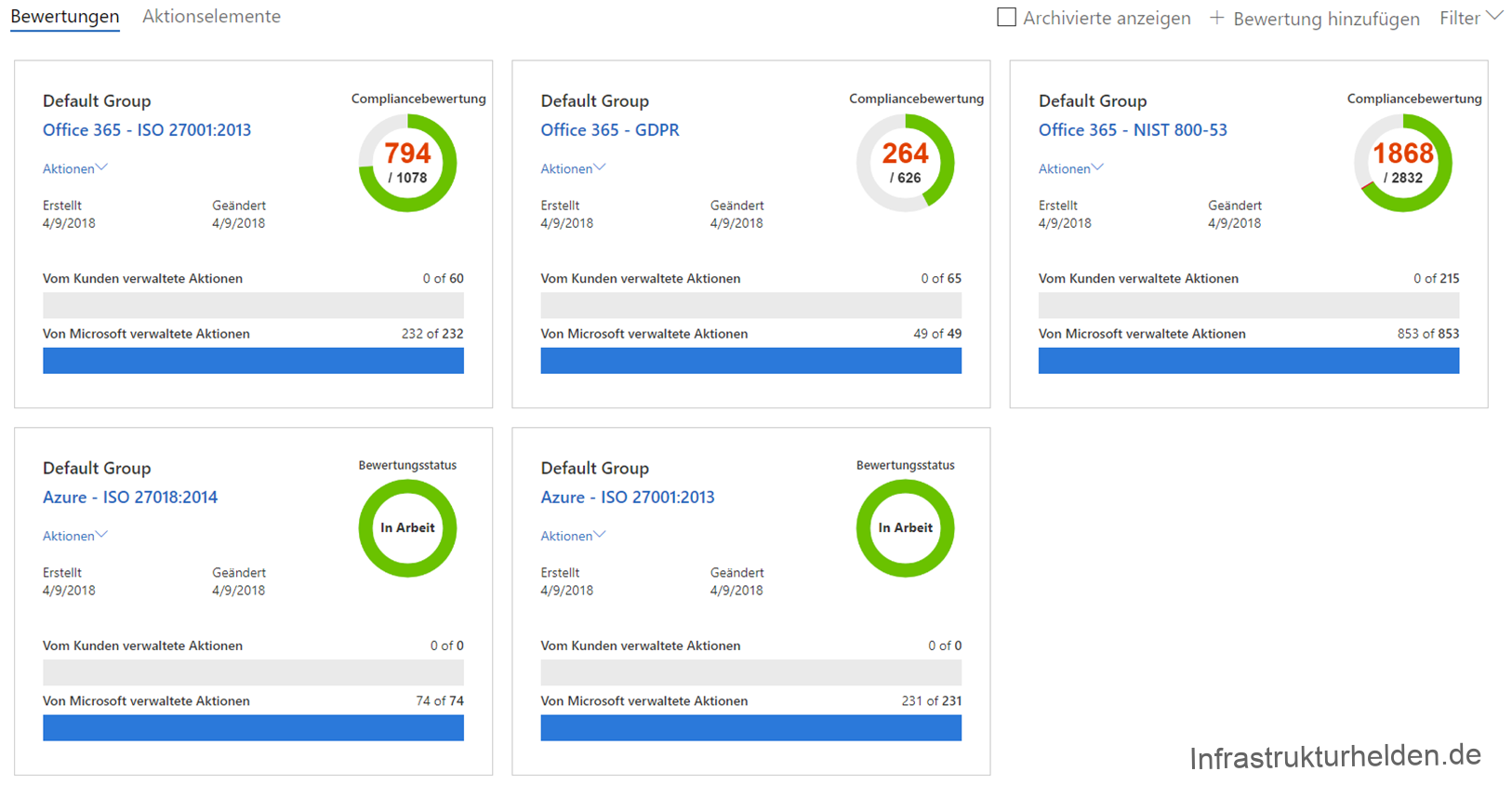
The Microsoft Cloud and Data Protection
Since the GDPR / DSVGO introduction, the topic of data protection, privacy and compliance is still a topic with which many lawyers still earn money. The problem, in my opinion, the technical reality distance with that the whole was designed. Not to be kept silent of the fact that the exceptions to the law were not delivered equally. But all this does not help us, we have to follow it. But I would not like to hold up you too much with my personal opinion to the GDPR. We look at ourselves what Microsoft offers us at tools.
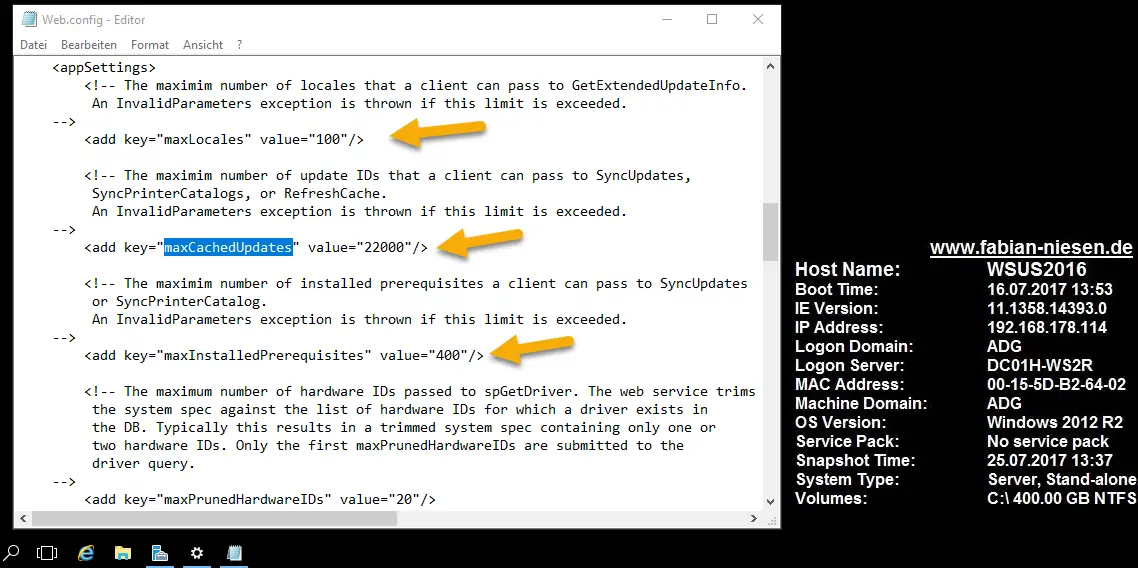
Problems with the Windows Server Update Service – 0x8024400D
I recently had an interesting phenomenon in a rather extensive environment. With a newly installed WSUS Server based on Windows Server 2016, some clients encountered errors “0x8024400D”. The clients were previously connected to an old WSUS on Windows Server 2008R2. Strange, there everything worked…
The usual attempts to reset the WSUS client, for example, brought no improvement. So I asked Google.
Local Administrator Password Solution (LAPS)
In the past, a company-specific standard was usually always used for local administrator passwords. But what do you do if an employee who knows the default password leaves the company?
Right, it should be changed. In the past, Group Policies (GPO) were often used for this, even if the password was in clear text in SysVol. This was fortunately stopped by Microsoft. What other solutions are available? In practice I have seen VBS or PowerShell scripts, the good ones have random passwords, the bad ones only a standard.
But isn’t there a well designed solution from Microsoft? Yes, there is, Local Administrator Password Solution (LAPS).