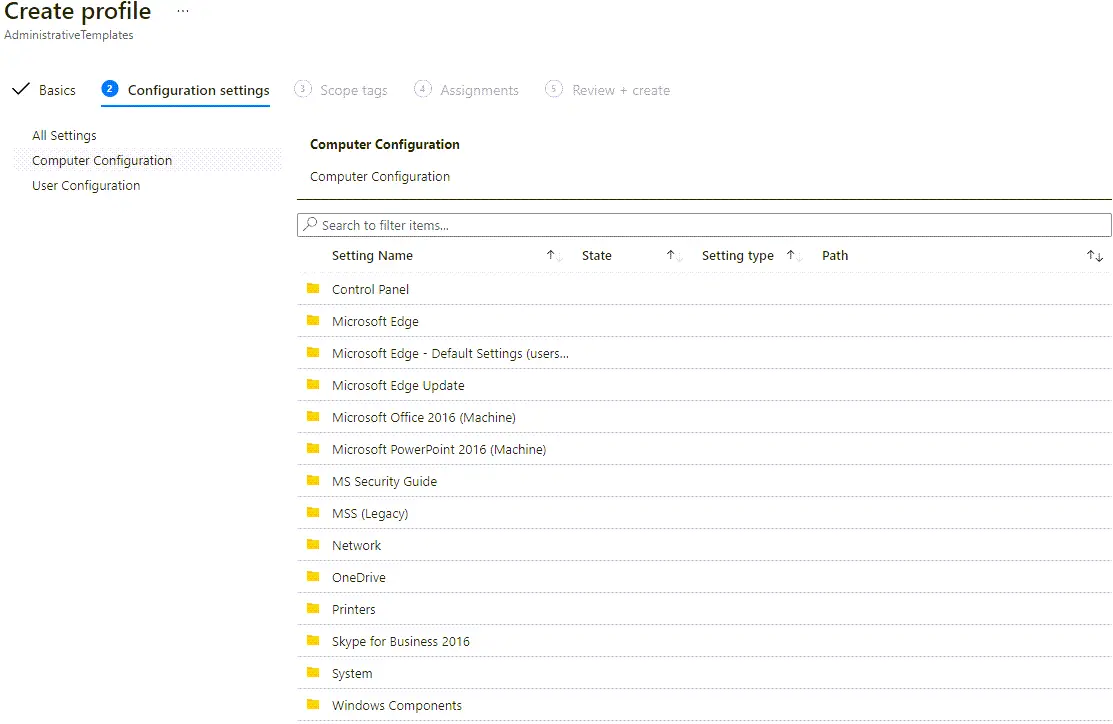
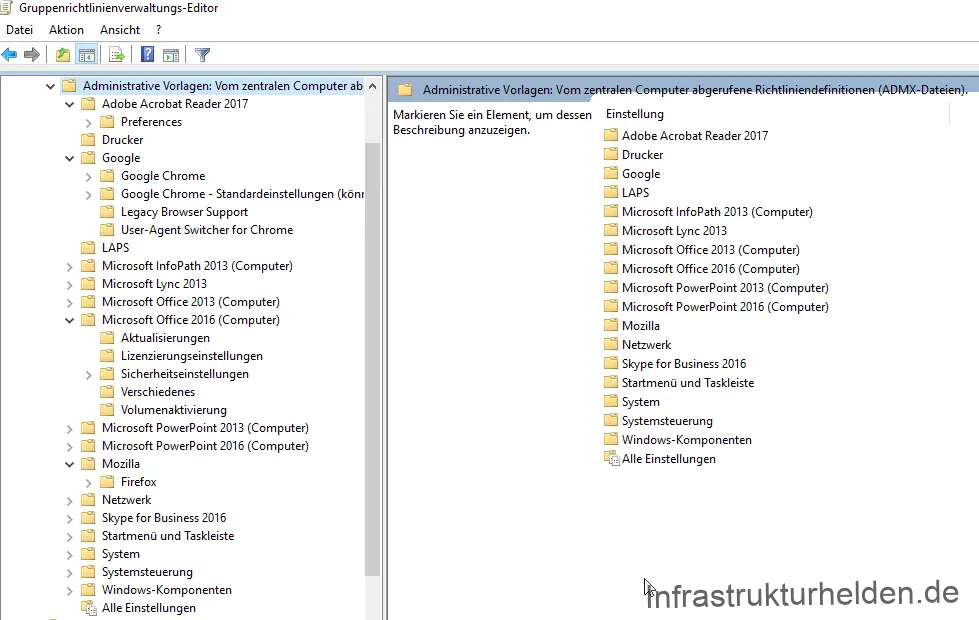
Active Directory group policies, also called Group Policy Object (GPO), are one of my core topics. I have a lot to do with this in various projects and as a Microsoft trainer. As a result, I have accumulated a number of templates and links. This link collection should make your search a little easier. Only templates of the respective manufacturers or projects are listed here. I have deliberately avoided third-party guidelines.
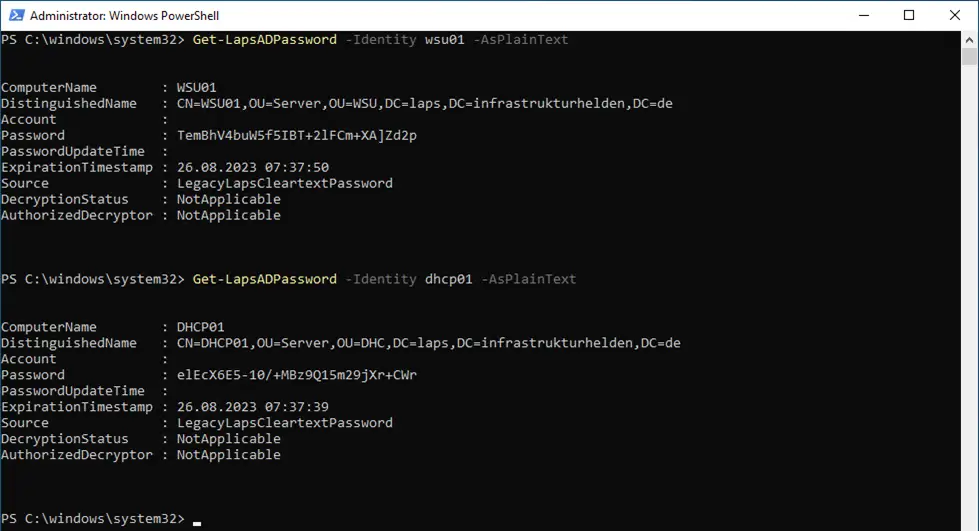
Windows LAPS and the migration from Microsoft LAPS
- Diesen Artikel auf Deutsch lesen. -In this era, the topic of IT security is becoming more and more important. A possible attack vector has always been the local admin passwords. In most cases, these were hard-wired into the installation image and had not been changed for years. Not only a risk from former employees. The lateral movement also poses a … Read more